IBSS has been approved by The Cyber AB as a CMMC Level 2 C3PAO and is currently accepting new assessment appointments. Connect with our experts to begin your certification journey.
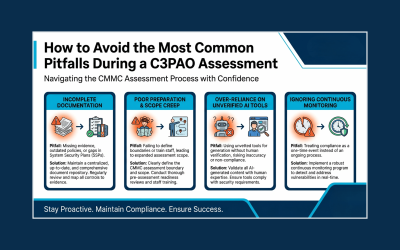
How to Avoid the Most Common Pitfalls During a C3PAO Assessment
Ensure a smooth CMMC Level 2 assessment with IBSS. Discover key pitfalls to avoid and schedule your objective, professional C3PAO assessment today.
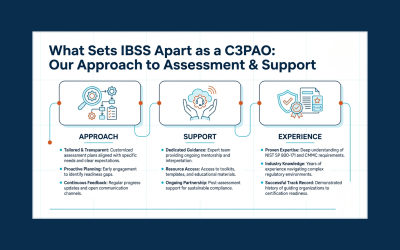
What Sets IBSS Apart as a C3PAO: Our Approach to Assessment and Support
Discover what sets IBSS apart as an Authorized C3PAO.
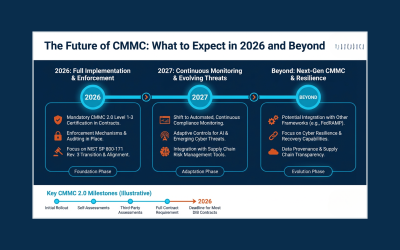
The Future of CMMC: What to Expect in 2026 and Beyond
IBSS, an Authorized CMMC Level 2 C3PAO, breaks down what contractors can expect from CMMC in 2026 and beyond. Explore key trends and schedule your assessment.
Strengthening Security and Trust with ICAM Solutions from IBSS
IBSS provides expert ICAM services; protecting identities, managing access, and enforcing Zero Trust security for agencies and businesses.
Building a Culture of Security Awareness
Learn how IBSS builds a culture of security awareness, empowering employees to protect data, systems, and mission-critical operations.
Cybersecurity and Artificial Intelligence: A Change in the Defense and Threat Landscape
By Saadia Shah Over the past 5 years, artificial intelligence (AI) has undergone a significant transformation in both professional and personal realms. Within the cybersecurity domain, AI has become a powerful tool for attackers to automate and refine their attacks,...
When Data Meets the Storm: How Historical Records Help Predict Tomorrow’s Weather
Discover how IBSS and NOAA use over a century of precipitation data to predict future weather and strengthen community resilience.
How the IBSS Volunteer Committee Supported the Back-to-School Season
IBSS’ Volunteer Committee supported teachers and schools this back-to-school season with donations, supplies, and community initiatives.