Are You Prepared for a Tornado?
Having a reliable source of weather updates is critical. A NOAA Weather Radio can provide real-time alerts, even if power or cell service is lost.
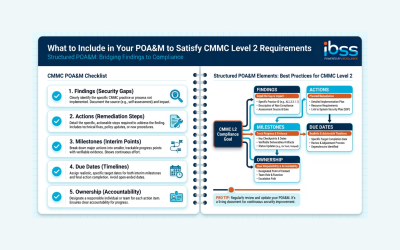
What to Include in Your POA&M to Satisfy CMMC Level 2 Requirements
Create a compliant POA&M for CMMC Level 2 by understanding what assessors expect. Learn the essential elements—controls, remediation steps, timelines, and resources—to align with NIST SP 800-171 and strengthen your path to certification.
CMMC vs. NIST SP 800-171: What’s the Difference?
Confused about the difference between CMMC and NIST SP 800-171? Learn how they relate, why both matter, and what your business needs to stay compliant.
In Search of the Perfect Bite – Geoduck Fritters and Black Bean Clams
Leaving geoducks in their “home” is important because if you are not going to eat a geoduck, please let it live in peace for the rest of its 140+ years.
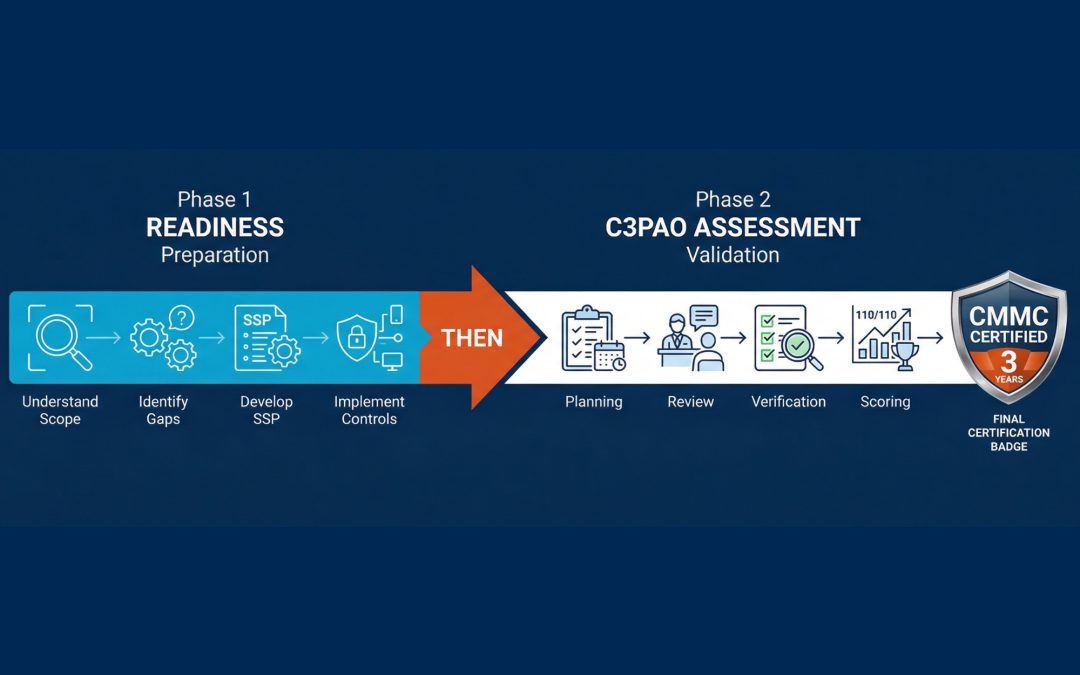
What Is a C3PAO and Why Does It Matter for Your CMMC Certification?
Not sure what a C3PAO is or why it’s critical to your CMMC success? Learn why you’ll need one to achieve Level 2 certification as a DoD contractor.
CMMC 2.0 Explained: What DoD Contractors Need to Know in 2026
CMMC 2.0 is here…are you ready?
The Threat of Space Weather
Though the Sun is almost 100 million miles away, it greatly influences our daily lives. Space weather refers to conditions in space that result from the Sun’s activity. While space weather might sound like a distant concern, it has real-world implications for critical systems.
In Search of the Perfect Bite. The Merroir of Seafood: Onaga (Long-Tailed Red Snapper) – Our Valentine’s Day Edition
With its striking appearance and exceptional taste, the Onaga is a true treasure of the Hawaiian waters. Its delicate texture and mild flavor, complemented by the unique sweetness derived from its diet.
Total Assure, an IBSS Company, Partners with Breacher.ai to Combat the Rise of AI-Powered Deepfake Threats
Together, Total Assure and Breacher.ai are providing businesses with actionable defenses to counter AI-driven threats that traditional security measures fail to address.